Many organizations are utilizing containers. Our new infographic “The Future of Containers” illustrates the benefits and projected growth of container technology.
Is your company thinking about going green? In our latest infographic, we share the benefits of Green IT.
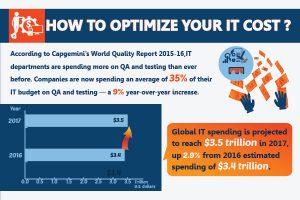
Is your organization starting to plan your IT budget for 2018? Before you finalize your plans review our “How to Optimize your IT Cost?” infographic. The infographic provides information on annual IT spending, ideas to optimize your IT cost, and more.
Ransomware is a growing threat to organizations. In our featured infographic we highlight the staggering growth of ransomware attacks.
Being that 2018 is right around the corner companies are now solidifying their IT budgets. Gartner Worldwide IT Spending Forecast projects IT spending will grow 4.3% in 2018. The report also provides a great snapshot of changing trends. For instance, organizations are expected to spend 7% more on enterprise software. In 2018, spending on data center systems is expected to decrease by 1.6%. How can companies optimize IT costs without sacrificing security and technology updates? According to Gartner, transparency and collaboration are at the core of optimizing IT cost. The […]